Does a Mac Computer Need Antivirus Software in 2025?
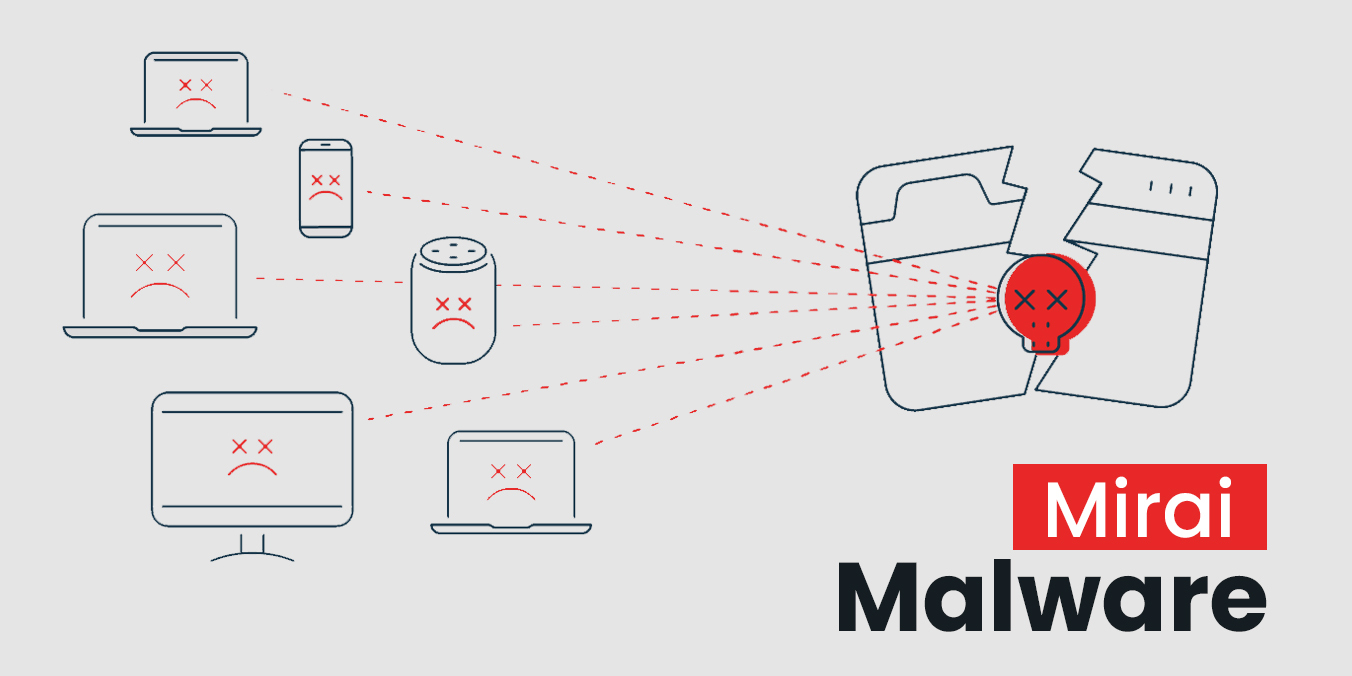
In recent years, the long-standing notion that Mac users are inherently prone to malware and viruses has been a rising concern. Indeed, macOS provides powerful protection against such security th....
















.jpg)
.jpg)